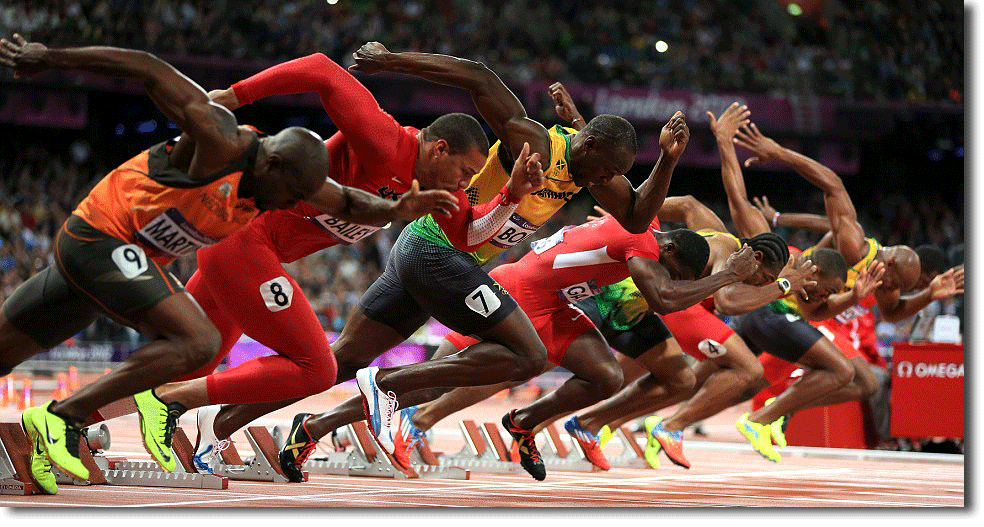
Jumping the gun
Note: In keeping with the AIRA Chatham House Rule policy the first example of the following article is unattributed. The below mentioned “Local Company” has assisted AIRA in writing the article, with the view to support and further educate fellow AIRA members, and enhance best practice Investor Relations. We thank them for this valuable contribution…
At the recent Sydney Australasian Investor Relations Association (AIRA) Chapter lunch, one of our corporate members recounted an instance of inadvertent early disclosure of a results announcement via its company website. In this article, we discuss the circumstances that led to this situation, highlight a similar instance from overseas, look at how this is something that could increasingly be an issue given changes in technology, and suggest some key learnings for investor relations and communications professionals.
Local Example
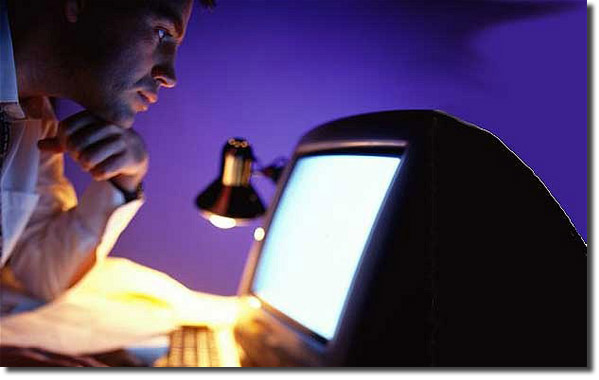
The company was finalising its results presentation the night before release of the results to the market… as is not uncommon for many AIRA members. The presentation, along with market announcement and financial statements were due to be signed off by the board early the next morning so all documents could be filed with the relevant exchanges before market open.
IR, Communication and Finance people were working on the presentation in the same room, emailing the document between each other and finalising it to prepare for publication. This included the Communications person uploading the slide deck to the back end of the company’s investor website ‘in development mode’, which meant it was not accessible by anyone browsing the website. i.e. no link was created to indicate “click here to download our HY16 Results” so the file was considered to be effectively ‘hidden’. In the past, there had been no issue using the development part of the website, which was hosted by an external software company…however, in this instance this approach exposed a significant risk.

Unknown to the company a pdf of the presentation was indexed to a link that could be accessed externally and a Bloomberg news bot had scraped the company website afterthe document was uploaded. In spite of the company website having no clickable link to the document, the Bloomberg bot had downloaded the pdf, named it correctly and posted it to the Current News page of the company’s equity section on the Bloomberg network i.e. <XXX AU> <Equity> <CN> <Go>. This occurred after the market had closed but some 12 hours before it was planned to be approved by the board and released to the exchange.
The company was only made aware of this when contacted by a sell side analyst, who was still working, received a Bloomberg alert and downloaded the document. He rang the IRO to confirm it was the latest, correct version. The version he referred to had only been changed by the CFO and IRO approximately 5 minutes earlier!
Initially it was thought that in emailing the slide deck to each other one of the three working on the presentation had inadvertently emailed it to someone externally, who had leaked it to Bloomberg. But that was quickly (and frantically) discounted. The IRO quickly went into Crisis Management mode, escalating the issue to the CFO and CEO in accordance with best practice.
The Bloomberg help desk in Singapore were reached after numerous attempts of using the <HELP> function on the company’s terminal. They were helpful and agreed to pull the document from the system having understood the situation and the fact the document had not been authorised to be released. However, the Bloomberg team warned the company that once the document was pulled the bot was still active so it had continued to scrape the company website for the presentation and the link needed to be removed completely. The company’s entire website had to be taken down to make sure the document wasn’t still there to be scraped by the bot. Bloomberg were eventually able to provide the problematic link to the document on the company’s website when the IRO and Communications people were unable to find it by looking at all external facing links.
In the time that the document was live on Bloomberg it had been downloaded three times: once by the analyst, once by the company, and once by someone else, who to this day is unknown. The company sent an email to the analyst that night indicating that Bloomberg had received the presentation in error, was not authorised to do so and the analyst should not rely on any of the information in it being correct.
Lessons learnt:
- Preparing the documents after market closed was ultimately the only thing that saved the company from having to make an unplanned disclosure when the document was leaked
- Analysis indicates that there are a large number of cases when bots are sweeping corporate websites for new or sensitive information
- Documents should only ever be uploaded to a website (or even test website) after they are confirmed live on the exchange – a delay of a few minutes to ensure the document is already public is ultimately a better outcome
- Some companies use a direct link to the exchange releases on their own investor site to eliminate all risk around uploading documents – this may remove the ability to customise the look and feel of the investor site but is ultimately fool proof against documents being leaked early
- Make sure that you have a plan in place to manage a situation where sensitive information or documents are inadvertently released
US Example – by Dean Laffan – iReport
Analysts following a certain stock which we’ll call ‘Newco’ were preparing for the release of Newco’s Full Year Results. In reviewing Newco’s previous releases in the days prior to the announcement and earnings call, the analysts noticed that the company was quite regimented in how they named the PDF files released. Let’s say it was Newco’s FY15 Results that were about to be released, the previous three release documents had been named as follows;
Newco_HYR_15.pdf
Newco_FYR_14.pdf
Newco_HYR_14.pdf
From the above, it was reasonable to assume that the new file to be released the next day would be called ‘Newco_FYR_15.pdf’
The documents were also always uploaded to the designated section of Newco’s website, where the location url might have looked something like this;
www.newco.com/investors/downloads/SECFilings/
The analysts supposed that if Newco repeated the same procedure as previously used that they might upload the document before public release in the belief that since there was no direct link to the file, it would be safe. If so, it should be found at;
www.newco.com/investors/downloads/SECFilings/Newco_FYR_15.pdf
The two analysts ordered pizza and waited, refreshing the url every 10 minutes or so. Voila! at about 8:00pm the night before the release, once uploaded by Newco staff, the PDF file appeared in their browser and was promptly downloaded.
Once again, no direct link had been made to the file and it had not yet been released to the SEC, yet it was exposed.
Key take-aways from this example:
- It is imperative that you do not upload the files to your website in any way until after they have been confirmed as published on the ASX.
- Note, there is nothing inherently wrong with the predictable naming of Newco’s PDF files. Once released to the market, the ‘guessability’ of the file name is irrelevant. Obscuring the file name is not the answer, rather it is following proper procedure.
- Investigate the full ‘chain of custody’ for all your ASX releases, especially those documents that may originate or be handled outside of the investor relations or company secretary domain. For example, presentations generated in your business services or in-house design departments, where awareness of these issues may not be front of mind.
- Ensure that upload of the documents is done by a staff member suitably cognisant of the importance of keeping these documents offline until they have been properly released to market.
- Finally, also be wary of your website Content Management System (CMS) that may allow you to ‘schedule’ release of documents at a predetermined date and time. In most cases the PDF will actually be on the site and the link generated and published at the time you specify, but the PDF would still be discoverable in a fashion similar to the above. Have a candid conversation with your IT department to fully understand how your website works in this area.
Dean Laffan is the founder of iReport the one-stop shop for all your design, communication, staging and technical needs for the events on your IR calendar. See more at www.ireport.com.au and our webcasting arm at www.streamit.net.au
Dean has worked extensively in the PDF format for over 15 years and as a member of the Acrobat Global Advisory Board.